Account Settings¶
The Account Settings page allows you to manage your personal profile, enhance your security, and review your connection history.
To access your settings, click your name in the User Menu (top right of the navigation bar) and select Settings.

Use the left-hand menu to quickly navigate between the following sections:
General: Manage your profile, email, Personal Key, and linked organizations.
Security: Update your password and configure multi-factor authentication (2FA/Passkeys).
Active Devices: Review and instantly revoke currently connected sessions.
Authentication Logs: Track all login attempts to your Reemo dashboard.
Activity Logs: Review the technical details of your past remote desktop sessions.
General¶
Manage your personal information and Reemo identity.

Account: Update your Username and Full Name (optional), then click Update to save your changes.
Email Address: Enter a new login email and click Update email. A 6-digit verification code will be sent to the new address to confirm the change.
Personal Key: A unique key used to link remote computers to your account.
Organizations: View the workspaces you belong to and your current role (e.g., Member, Admin, Owner).
Delete Account: Permanently erase your Reemo account. Enter your password in the provided field and click Delete My Account to confirm.
Important
If your account is managed by an organization (Managed user account), you cannot change your personal information or delete your account.
If you are an Owner of an organization, you cannot delete your account until you transfer ownership.
Security¶
Protect your account by managing your credentials and enabling multi-factor authentication (2FA). Two main actions are available:
Enable or disable Two-Factor Authentication (2FA) to secure your account with an authentication app.
Change your Password by entering the old password, then the new password to confirm.
Note
Multiple 2FA methods can be enabled simultaneously.

Two-Factor Authentication (2FA)¶
This section displays whether 2FA is currently enabled or disabled on your account. To activate it, click one of the following buttons to open a dedicated setup page.
Enable with Authenticator App¶
When you choose to enable 2FA with an Authenticator App, a sub-page appears to finalize the registration of your authentication device.
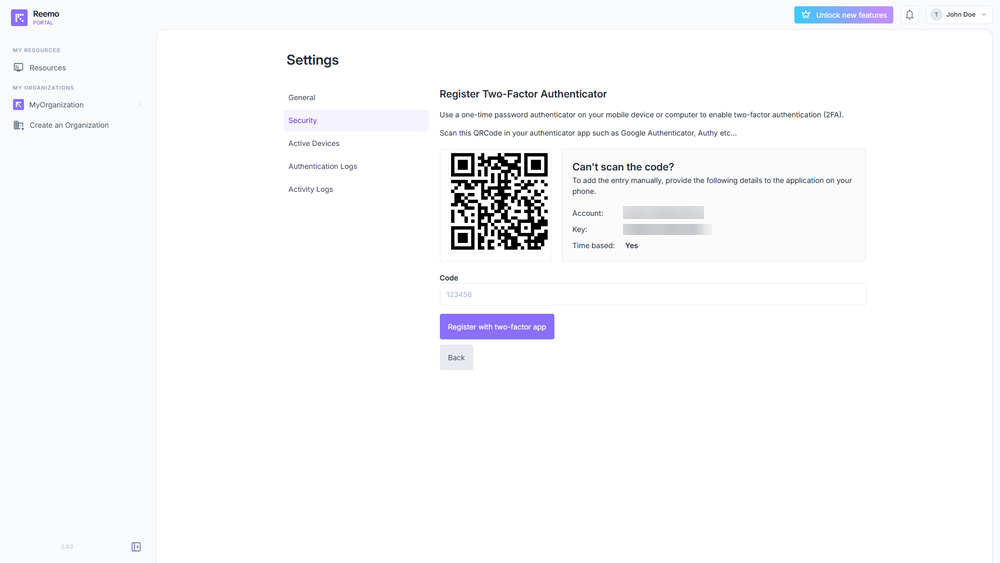
Sub-page for setting up two-factor authentication via Authenticator App.¶
Two methods are provided to link your account to an application such as Google Authenticator or Authy:
QR Code: Scan the displayed code with your app.
Account + Key: If you cannot scan the code, enter the provided information manually.
Once the app is configured, enter the one-time code generated in the Code field, then click Register with two-factor app to confirm.
Important
Two-factor authentication adds an extra layer of security to your account. Even if your password is compromised, unauthorized access will be blocked without the code generated by your authentication app.
Enable with Passkey¶
When you choose to enable 2FA with Passkeys, a sub-page appears to finalize the registration of your authentication device.
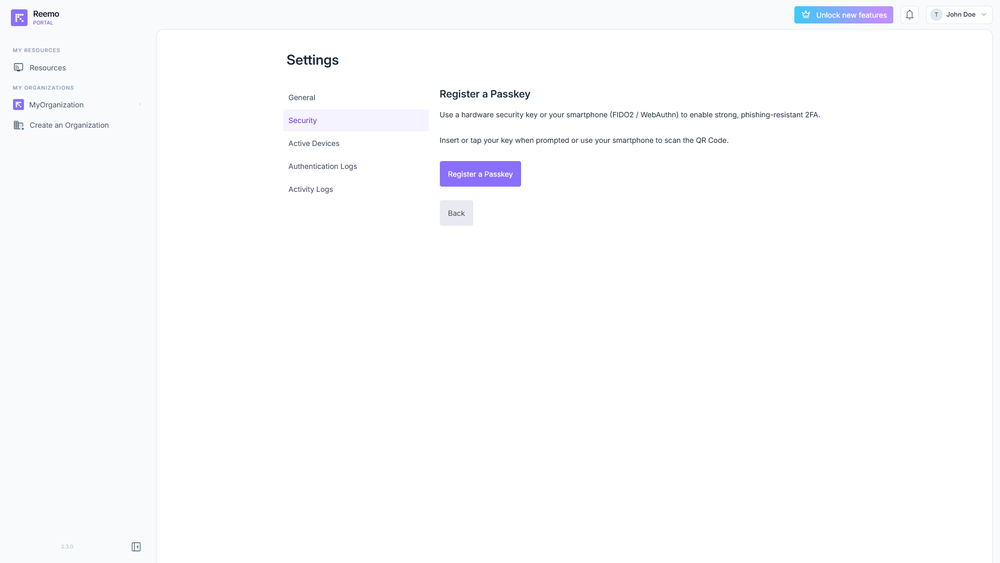
Sub-page for setting up two-factor authentication via Passkeys.¶
Follow the instructions provided by your browser to create and register a new Passkey. Once the Passkey is created, it will be securely linked to your account for future authentication.
Important
Passkeys add an extra layer of security to your account. They do not replace your password but work alongside it to provide stronger protection.
Note
Change Password¶
Update your credentials by entering your current password, followed by your new password.
Active Devices¶
The Active Devices section displays the list of browsers and devices currently connected to your account. This allows you to check your active sessions and revoke those you do not recognize.

The Active Devices section displaying connected sessions, IP addresses, online status, and the browser used.¶
The available information for each session is:
IP Address: Public IP address used for the connection.
Status: Indicates whether the session is Current and whether the device is currently Online.
Last Access: Date and time of the last activity from this browser or device.
Browser + OS: Information about the software used for the connection (e.g. Chrome on macOS).
First Connection: Date and time of the first recorded login on this browser.
A Revoke button allows you to end an active session. This action immediately disconnects the corresponding browser or device.
Note
Use this section to monitor access to your account. If you notice an unknown or suspicious session, revoke it immediately to secure your account.
Authentication Logs¶
The Authentication Logs section allows you to review the history of login attempts to your account. Each entry provides useful information to identify the origin and legitimacy of an access attempt.

The Authentication Logs showing connection history, including the date, IP address, browser, and operating system.¶
The available information for each authentication attempt is:
Date: Exact date and time of the login attempt.
IP adress: Public IP address used for the connection.
Browser: Browser used (e.g. Chrome, Firefox).
Operating System: Operating system used during the connection (e.g. Windows 11, OS X 10.15).
Note
This section is particularly useful for detecting suspicious logins. Regularly check the IP addresses, browsers, and operating systems to identify any unusual attempts to access your account.
Activity Logs¶
The Activity Logs section displays the history of your connections to remote computers and containers. It allows you to track your past sessions and get detailed information about their duration, the machine used, and the type of connection established.

The Activity Logs displaying past sessions and their technical details.¶
The available information for each session is:
Date: Date and time of the connection.
Computer: Remote computer or container to which the session was opened.
Duration: Total duration of the remote session.
Organization: Organization the machine belongs to (empty if the machine is a personal computer).
Computer IP: Public IP address of the remote workstation.
Client IP: Public local IP address of the device that initiated the connection.
Connection Type:
direct/udp: Direct connection (Highest performance).relay/udp: Connection routed via a relay server over UDP.relay/tcp: Connection routed via a relay server over TCP.relay/websocket: Connection routed via a relay server over WebSocket (Fallback).
Note
This section helps you understand the quality of your connections and identify potential network issues. A direct/udp status is recommended for better performance.